E-Shodhpatra : A Preserve Intellectual Data
4.7
(725)
Write Review
More
$ 18.99
In stock
Description

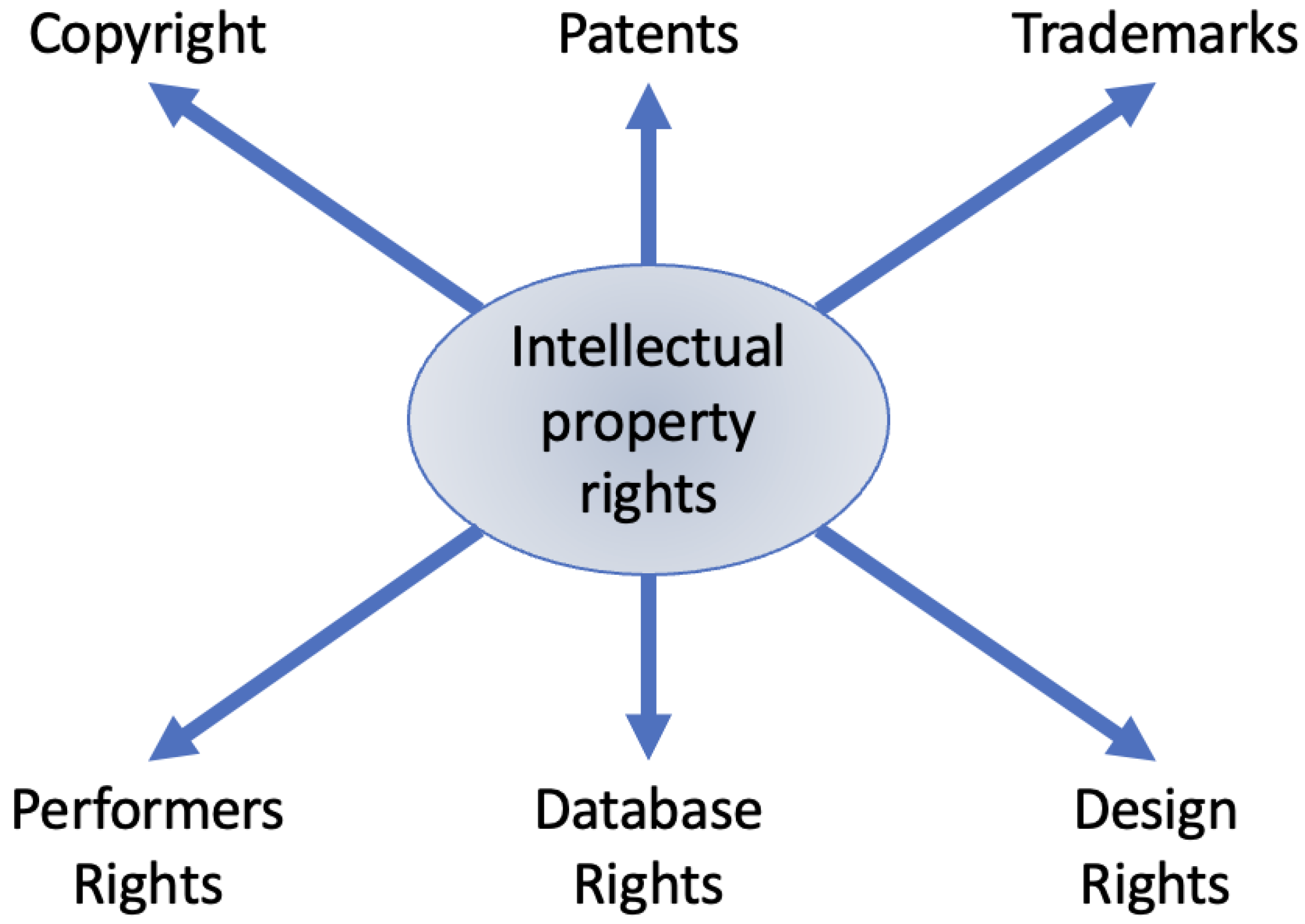
The Exploitation of Intellectual Property Rights
Data Origination: Human-Centered Approach for Design, Acquisition
Algorithms, Free Full-Text
PDF) Introductory Chapter: Data Privacy Preservation on the

PDF) Critical reflections on Big Data security and Intellectual

PDF) Critical reflections on Big Data security and Intellectual
The IET Shop - Cognitive Sensing Technologies and Applications

PDF) The Semantics of the Ergative in Nepali

Best practices of Managing GDPR with snowflake
Related products
You may also like