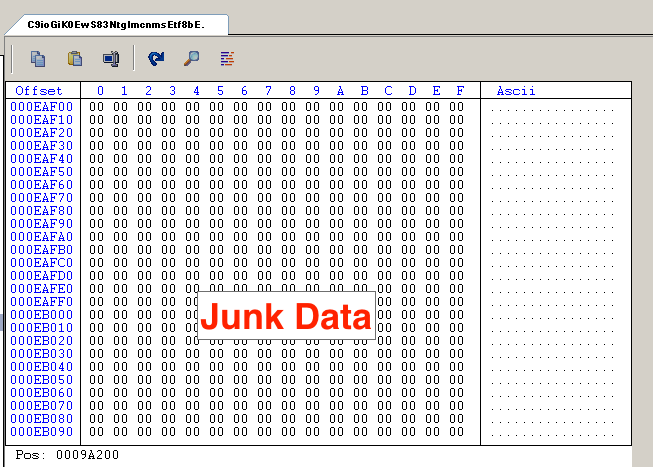
How Hackers Use Binary Padding to Outsmart Sandboxes
4.5
(629)
Write Review
More
$ 25.00
In stock
Description
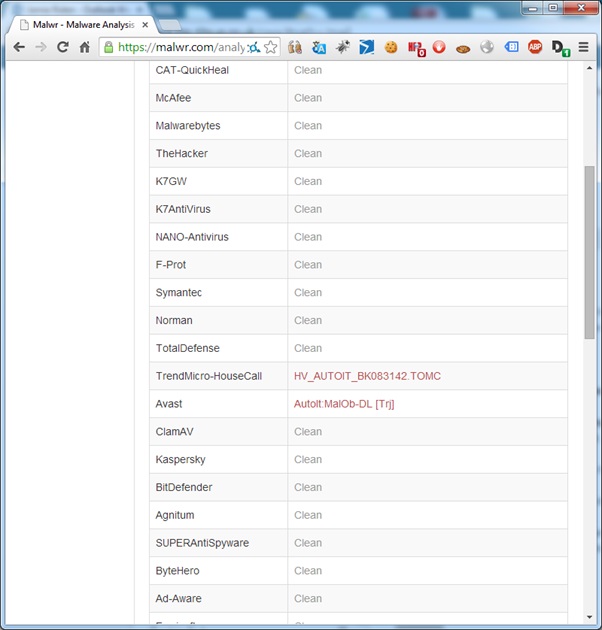
Quick and dirty binary analysis using sandboxes

Misconfigured Airflows Leak Credentials from Popular Services

Emre KISA on LinkedIn: Create and manage custom detection rules in

Factors to Consider When Choosing a Cloud Workload Protection Platform

نشر Emre KISA على LinkedIn

How Hackers Use Binary Padding to Outsmart Sandboxes

Kaiji Goes Through Update but Code Reuse Detects It- Intezer

Roy Halevi (@royhalevi) / X

Roy Halevi (@royhalevi) / X
Related products
You may also like




:format(webp)/https://static-ph.zacdn.com/p/vero-moda-4254-7760103-1.jpg)

