Layer 8 Technology: How We Protect Users at our Plattsburgh Office
4.8
(299)
Write Review
More
$ 13.50
In stock
Description
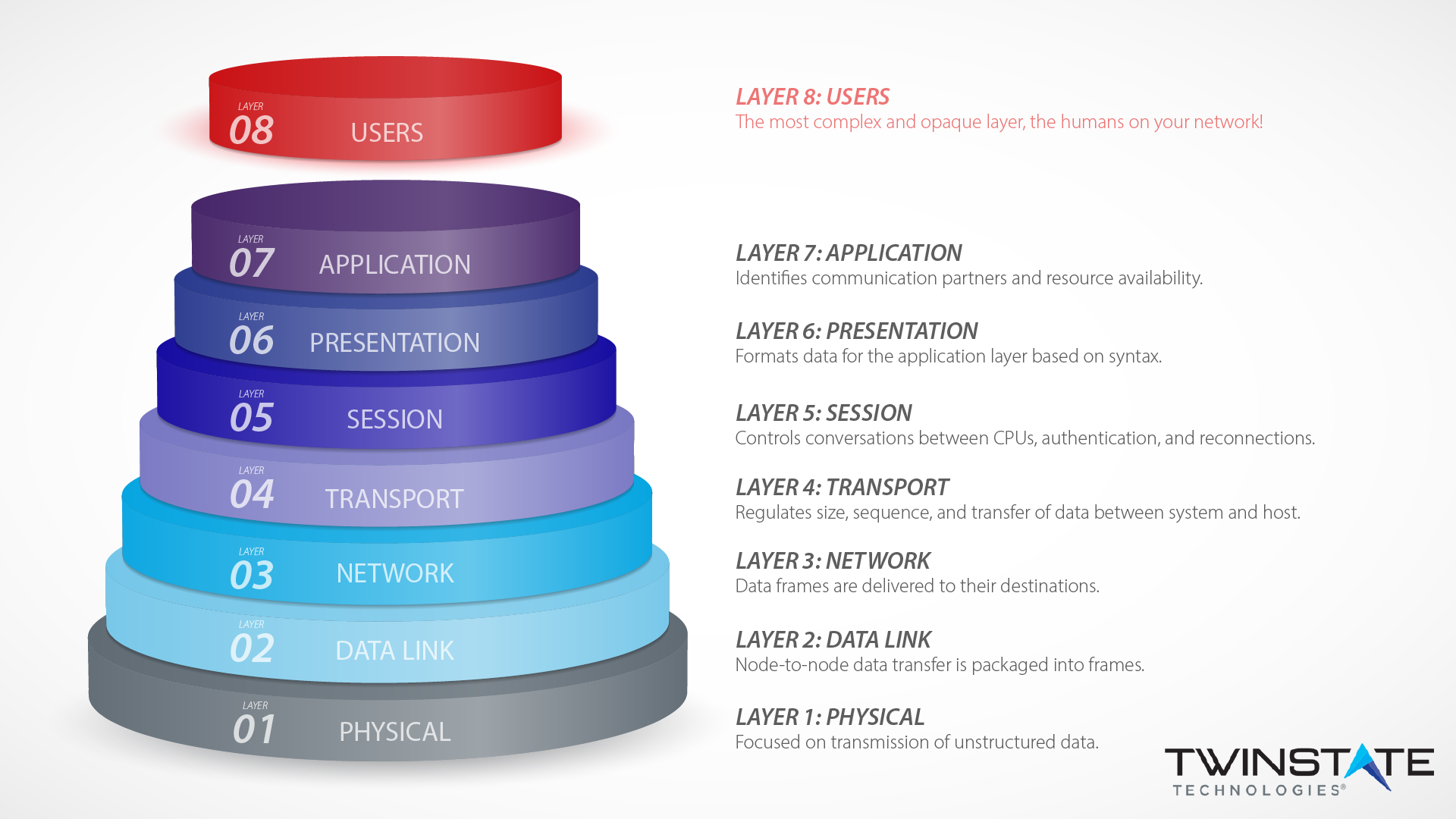
Layer eight security depends on end-users according to the OSI model. Learn how Twinstate Technologies protects the users at our Plattsburgh, NY office.

KPMG University Connection
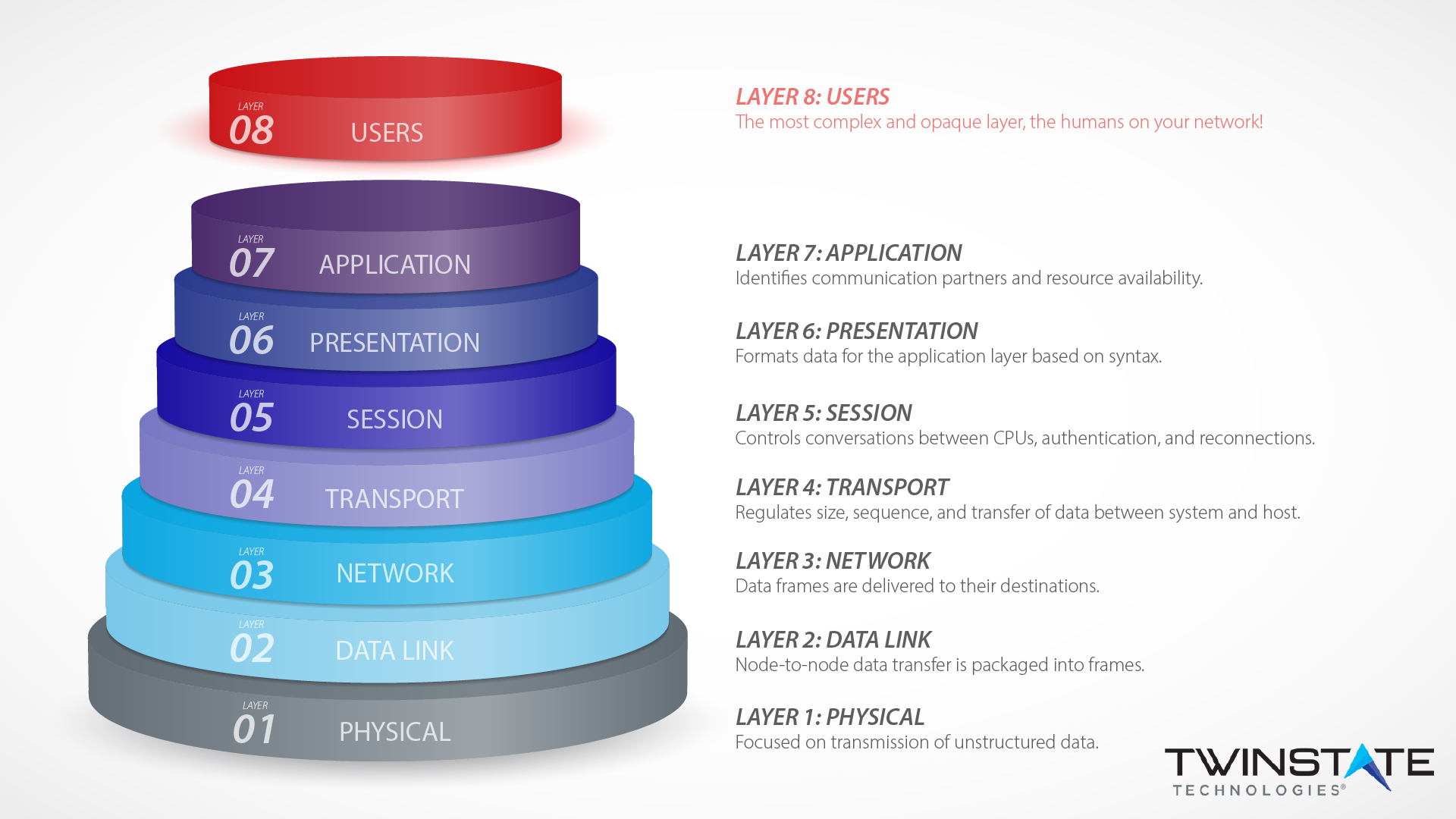
Layer 8 Technology: How We Protect Users at our Plattsburgh Office

Be More. Be Useful. Be of Service - 8Layer Technologies, Inc.

Online Cisco CCNP Enterprise: ENCOR & ENARSI from Champlain Valley

Bitcoin Mining Noise Drives Neighbors Nuts—a Giant Dentist Drill

How is technology transforming the workplace?

KEEPING THE FAITH: University of Richmond's first rabbi

LayerEight

Part IV - Case Studies Renewable Energy Guide for Highway

From Day One September Virtual: New Ideas for Successful

Managed Security Services - Incident Response
Lost in transplantation - Reveal
You may also like